The power of threat intelligence
In the world of cyber threats, knowledge is your greatest weapon. Threat Intelligence opens the door to secrets hidden in the digital shadows – insights into the minds of adversaries, their every move, and their next steps. It’s like having a crystal ball for cybersecurity, empowering you to outsmart threats before they strike. Illuminate the darkness, harness the power of threat intelligence, and guard your digital kingdom.
Threat Intelligence
In many cases, credentials and access to your infrastructure have already been gained through mass phishing campaigns, browser exploits, and drive-by downloads. These credentials and access points are then sold on the dark web. BuddoBot monitors the places where this valuable information can end up. We inform you of these leaks and use them as an adversary would, chaining them with other methods to gain privileged access and offer valuable insights into your hidden vulnerabilities.

Key Components
- Data Collection: Intelligence begins with gathering data from various sources, including open forums, dark web channels, and insider reports.
- Analysis: Once we have the data, we analyze it to identify credential and access threats to your organization. It’s like deciphering a code to understand your enemy’s intentions.
- Contextualization: Understanding the context of these disclosures is key. Is the threat nation-state-sponsored, financially motivated, or something else entirely? We focus on what each identified breach could mean for your organization, deciphering adversaries’ plans.
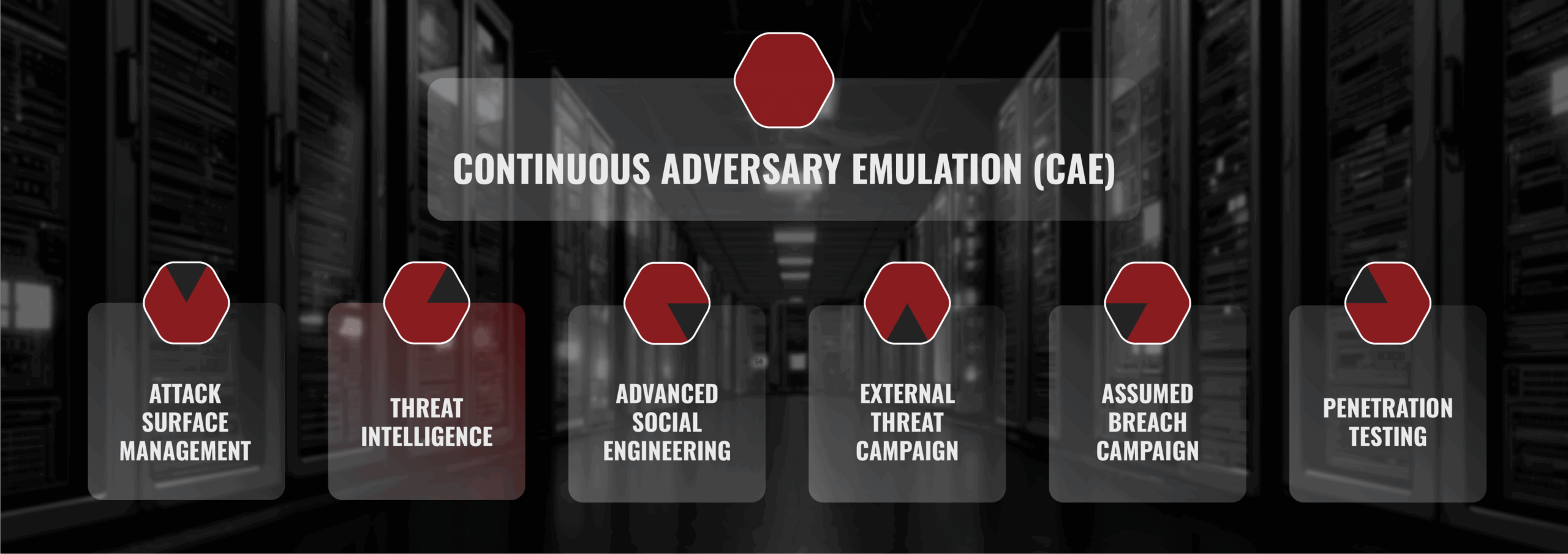
Critical to Adversary Emulation
Threat Intelligence and Continuous Adversary Emulation (CAE) are not standalone practices; they complement each other in critical ways:
- Targeted Simulations: Armed with threat intelligence, CAE can simulate specific threats that your organization is likely to face. It’s like training your defenses for a battle you know is coming.
- Realistic Emulation: Threat intelligence provides valuable insights into an adversary’s tactics and techniques. Our CAE team uses this information to create highly realistic attack scenarios.
- Proactive Defense: By combining the two, your organization can move from a reactive stance to a proactive one. You’re not waiting for threats to happen; you’re actively preparing for them.
- Customized Strategies: Threat intelligence allows us to tailor your CAE campaigns to mimic the exact threats your organization may encounter, making your defenses highly targeted.