Deceptive threats are very real
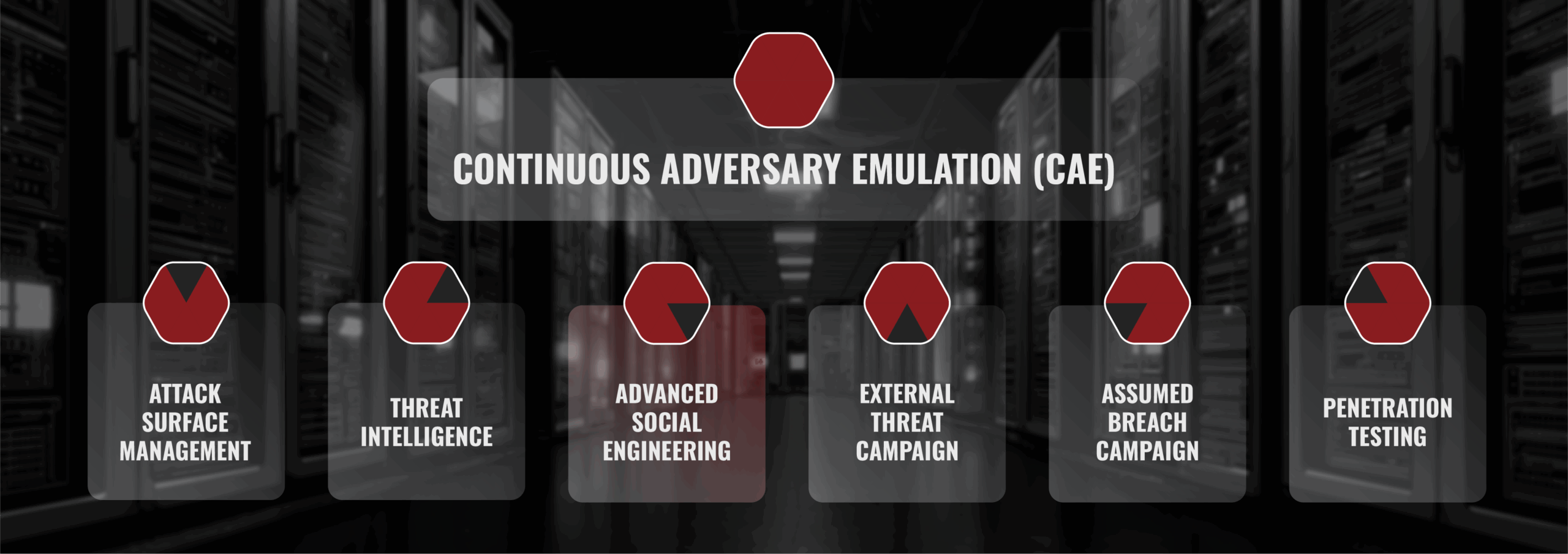
Welcome to the shadows of the digital world, where hidden threats lurk and our vulnerabilities are exploited. In this interconnected world, technology is intertwined seamlessly with our everyday lives and we find ourselves vulnerable to a vastly growing breed of cyber threat: social engineering. Social engineering is a cunning game of manipulation that preys on human trust. It operates on the premise that humans are often the weakest link in the security chain. Instead of directly exploiting technical vulnerabilities, social engineers manipulate human psychology to perform malicious actions or gain unauthorized access to sensitive information. Social engineering is a critical component of BuddoBot’s Continuous Adversary Emulation (CAE) service, helping identify how staff might be vulnerable so you can enhance essential security practices for your workforce.

We Are Human
Advanced social engineering allows us to navigate this complex landscape with greater security and trust. By delving into the intricacies of human psychology and behavior, we can proactively identify and address potential threats, protect sensitive information, and build stronger, more resilient communities. It’s about turning the tables, using our understanding of human nature as a shield, and fostering a safer digital environment for everyone. Embracing advanced social engineering is not just a necessity; it’s an eye-opening opportunity to fortify our digital lives and safeguard the future.
Advanced Social Engineering
Advanced adversaries require advanced solutions. In the realm of advanced social engineering services, we dive into the minds of cybercriminals.
With our industry experience in the offensive and defensive fields, we know that one of the largest contributors to breaches is the social engineering of employees. Even industry best-practice defenses like two-factor authentication (2FA), mail filtering, and end-point protection can fail. Employees and partners are the main in-roads to privileged access.
As one component of our CAE, BuddoBot uses cutting-edge phishing and vishing techniques to target your organization. These techniques include trusted sender domains, spear phishing/vishing using OSINT, custom pretexts, 2FA proxies, 2FA bombing, template injects, AI vishing profiles, custom file payloads, and a myriad of email security filter bypasses.

