How far does the rabbit hole go?
Once your security perimeter is breached, the next step is understanding the extent of an adversary’s capabilities and access. An assumed breach campaign uncovers crucial information surrounding the speed and effectiveness of your security team’s response. If you’re using a managed service provider, Endpoint Detection and Response, or Managed Detection and Response, how quick is their response within your organization? Do all automated security systems and software respond and issue alerts as expected? What if one of your security teams has an adversary employed? What do they have access to?
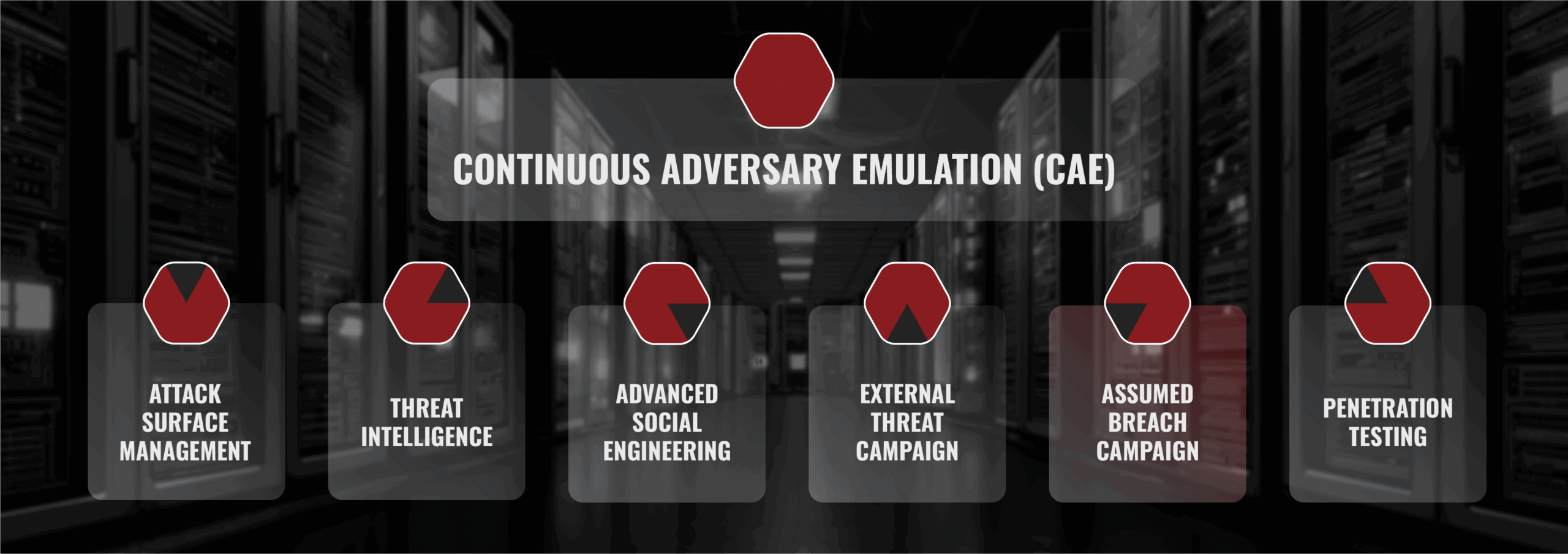
Elements of Assumed Breach Campaigns
- Realistic Scenario Simulation: These campaigns simulate real-world attack scenarios, assuming that an adversary has already gained access to the network. This realistic testing helps organizations understand their vulnerabilities and how attackers might move within their systems.
- Incident Response Evaluation: One of the primary goals is to assess an organization’s incident response capabilities. How quickly can they detect the assumed breach, and how effectively can they contain and remediate it?
- Continuous Learning: Assumed breach campaigns are not one-time events. They are an ongoing commitment to learning from each exercise and applying those lessons to improve security measures.


Preparing for the Inevitable
BuddoBot’s assumed breach campaign is designed to emulate post breach and/or insider access and evaluate the readiness of internal security controls and processes.
The reality is that there will always be new exploits against technology, premises, and employees:
- Zero-Day exploits like Heartbleed and log4j will continue to be discovered.
- Social Engineering attacks and tools continue to grow in sophistication.
- Even in the most secure organizations, the possibility of an insider threat exists.
- Even something as innocuous as a meeting room ethernet jack can give privileged access.
In order to anticipate such scenarios, our assumed breach campaign operates under the assumption of a potential breach and deploys our offensive security engineers within the internal network. This type of testing is beneficial for organizations that have already established a strong external security system. It saves time by directly addressing the organization’s readiness in the event of a breach.
Industry Standard Approach
In our assumed breach campaigns, we leverage two methodologies. In the first methodology, we execute industry standard red team and penetration testing methodologies. This includes, among other things:
- Access through manipulation of protocols and technology
- Credential theft, brute force, and cracking
- Privilege escalation
- Pivoting through advanced Windows or Linux networks
- Exploiting services
- Exploiting abuse primitives in Azure or O365
- Endpoint Detection and Response (EDR) / Antivirus bypass
While the above methodology is very technical and advanced, sometimes it doesn’t fully address current attacker tools, techniques, and processes. That’s where our Next-Gen Adversary Approach comes in.
Next-Gen Adversary Approach
This methodology is based on a mixture of certain MITRE ATT&CK framework modules and our experience with modern adversaries. These adversaries never install software, they hardly exploit, they avoid EDR, and they look like regular users to your security operations center (SOC). While not attracting any attention, they gather recon data and pile it up until they strike all at once – often too quickly for your SOC to respond.
Adversaries frequently have motivations beyond financial ransom. They may seek to disrupt your business for fun, simply because they can.
