Vulnerability scanning is NOT a PenTest
It is crucial for everyone to understand that a vulnerability assessment should not be mistaken for a penetration test. We, as passionate practitioners, are concerned by the vast misrepresentation of penetration tests within the market and the false sense of fortitude they provide. Our goal is to provide our customers with clarity around all that we do and an understanding that authentic penetration tests are valuable to organizations.
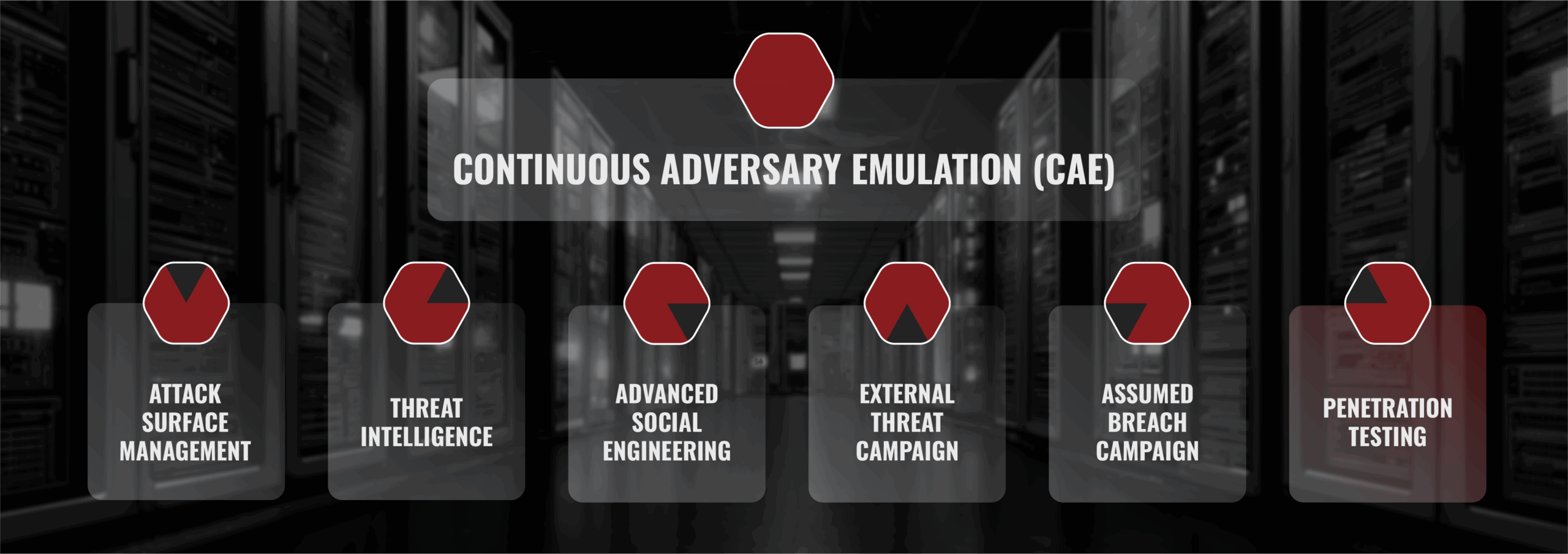
Compliance & Scoped Tests
The final component of the adversary’s playbook is their tenacious technical ability aimed at your technology. BuddoBot examines your entire threat profile to identify vulnerabilities that could accomplish adversary objectives. This includes applications, cloud, infrastructure, mobile, and more. While our goal is to accomplish a defined shared objective with the customer, our manual red team testing can uncover a vast gamut of security vulnerabilities. There are two components of this testing: our in-house developed security automation and our exceptional offensive security engineers.

Infrastructure Penetration Testing
- Remote administration services and protocols (VPN, SSH, RDP, FTP, IKE, ++)
- Technology administration web panels
- Cloud infrastructure configurations (Azure, GCP, AWS)
- Mail services (relays, OWA, O365)
- Known breached credentials

Our process is enhanced with both industry standard and homegrown vulnerability checks. It achieves finding known CVEs and custom fuzzing on application inputs. These are passed to our Offensive Security Engineers for validation and exploitation. No canned scans, no false positives.
Our offensive security engineers pour over the attack surface looking for misconfigurations and vulnerabilities that accomplish the campaign goals. Often, the difference in an offensive security team is its ability to find novel manual findings that are deeply embedded in the attack surface. As a baseline, we use common testing methodologies like OWASP, PTES, WAHH, etc., but are often more focused on finding logic flaws, authentication/authorization bypass, and exploitable injection vulnerabilities that really matter to a client.
Web Application Penetration Testing
When hacking web applications, the golden standard is covering things like the OWASP Top Ten vulnerabilities, using the OWASP Testing Guide. While we identify these vulnerabilities, we have also developed an in-house methodology for application testing that goes far beyond those resources.
View Our Methodology
-
Identification and OSINT analysis of all components of the stack:
- Server – open ports and services
- Web server software
- Application framework
- Custom or COTS code (most applications)
- Application libraries
- Server integrations
- Known CVE Analysis using our home-grown automation
- Deep manual security assessment specifically in these areas:
- Authentication
- Authorization
- Misconfiguration
- Persistent user input
- Multiple user levels
- Application Integration Functions
- Upload and export functions
- API calls
- Admin tools
- Dynamic parameters/paths
- Comprehensive content discovery:
- Historical link analysis
- Spidering
- Contextual brute force with recursion
- JavaScript analysis (paths, parameters, de-obfuscation, libraries)
- Thorough input analysis:
- Reflected content analysis
- Fuzz testing (dynamic parameters, REST API functions, XML, JSON, URL Parsers, File Uploads) for XSS, SQLi, SSRF, SSTI, LFI, Command Injection, and more.
- Logic, authorization, and access control issues:
- Stage bypass
- No authorization access
- Limited user access
- Broken SSO configuration
- Testing abuse primitives in applications
