Fortify your perimeter
Why take the risk of letting an enemy breach your defenses when it can potentially be avoided? Organizations make significant investments in robust defensive measures such as firewalls, IPS, software, antivirus programs, and managed security services – all designed to prevent unauthorized access from outside forces. Yet the missing piece for many organizations is validation, and that’s where external threat campaigns come in. It’s crucial to validate whether these investments are truly delivering the expected level of protection. Don’t leave it to chance – ensure that your investments in defense are truly effective in safeguarding your assets and data.
Breaches can be reduced...
External threat campaigns involve simulating cyber threats from external actors with the objective of assessing and improving an organization’s security defenses. Think of it as a controlled, real-world test where cybersecurity experts play the role of adversaries to identify vulnerabilities and weaknesses in an organization’s systems.
While automated testing can be a useful part of an adversary’s toolkit, we know that real adversaries often use more intricate and in-depth methodologies to breach their targets.

External Threat Campaign Goals
- Identify pathways to breach the perimeter and establish internal/privileged access
- Identify exploits to external infrastructure and applications for private data access
- Identify means to disrupt customer operations and cause monetary damage
Elements of External Threat Campaigns:
- Realistic Testing: By mimicking the tactics and techniques of real adversaries, organizations gain insights into how well their defenses can withstand actual cyber threats. This provides a more accurate assessment of their security posture.
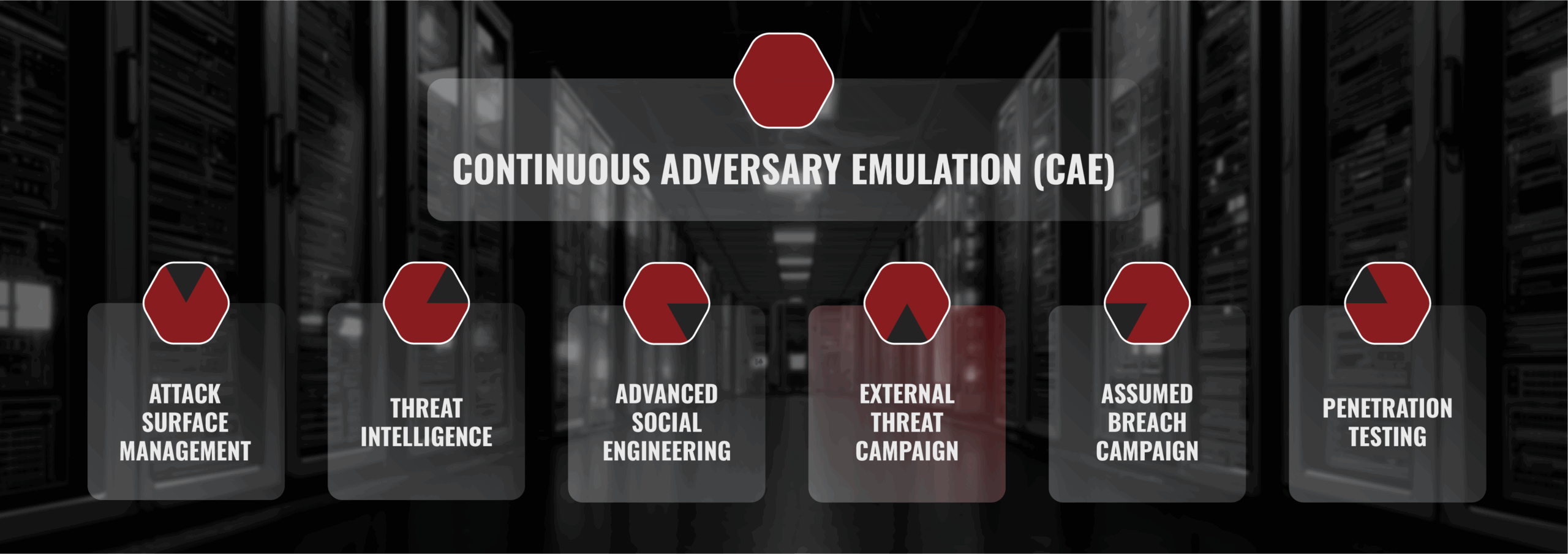
- Continuous Improvement: External threat campaigns are a key component to Continuous Adversary Emulation (CAE), as they are not one-time events. They are ongoing efforts that adapt to the evolving threat landscape. This allows organizations to refine and enhance security measures on a continuous basis.
- Detection and Response: These campaigns evaluate an organization’s ability to detect and respond to cyber threats in real time. This helps uncover gaps in incident detection and response capabilities, regardless of whether you have an internal response team or use an external security service provider.
- Risk Mitigation: Identifying critical vulnerabilities through emulation enables organizations to proactively address these issues. By fixing weaknesses or identified gaps, the risk of a successful breach is significantly reduced.
- Security Awareness: External threat campaigns serve as a powerful tool for educating employees about the potential impact of real cyber threats. This fosters a culture of security and preparedness within the organization.
